Introduction | Security snapshot | Threat briefing
Defending against attacks | Expert profile
Education is essentially an “industry of industries,” with K-12 and higher education enterprises handling data that could include health records, financial data, and other regulated information. At the same time, their facilities can host payment processing systems, networks that are used as internet service providers (ISPs), and other diverse infrastructure. The cyberthreats that Microsoft observes across different industries tend to be compounded in education, and threat actors have realized that this sector is inherently vulnerable. With an average of 2,507 cyberattack attempts per week, universities are prime targets for malware, phishing, and IoT vulnerabilities.¹
Security staffing and IT asset ownership also affect education organizations’ cyber risks. School and university systems, like many enterprises, often face a shortage of IT resources and operate a mix of both modern and legacy IT systems. Microsoft observes that in the United States, students and faculty are more likely to use personal devices in education compared to Europe, for example. Regardless of ownership however, in these and other regions, busy users do not always have a security mindset.
This edition of Cyber Signals delves into the cybersecurity challenges facing classrooms and campuses, highlighting the critical need for robust defenses and proactive measures. From personal devices to virtual classes and research stored in the cloud, the digital footprint of school districts, colleges, and universities has multiplied exponentially.
We are all defenders.

A uniquely valuable and vulnerable environment
The education sector’s user base is very different from a typical large commercial enterprise. In the K-12 environment, users include students as young as six years old. Just like any public or private sector organization, there is a wide swath of employees in school districts and at universities including administration, athletics, health services, janitorial, food service professionals, and others. Multiple activities, announcements, information resources, open email systems, and students create a highly fluid environment for cyberthreats.
Virtual and remote learning have also extended education applications into households and offices. Personal and multiuser devices are ubiquitous and often unmanaged—and students are not always cognizant about cybersecurity or what they allow their devices to access.
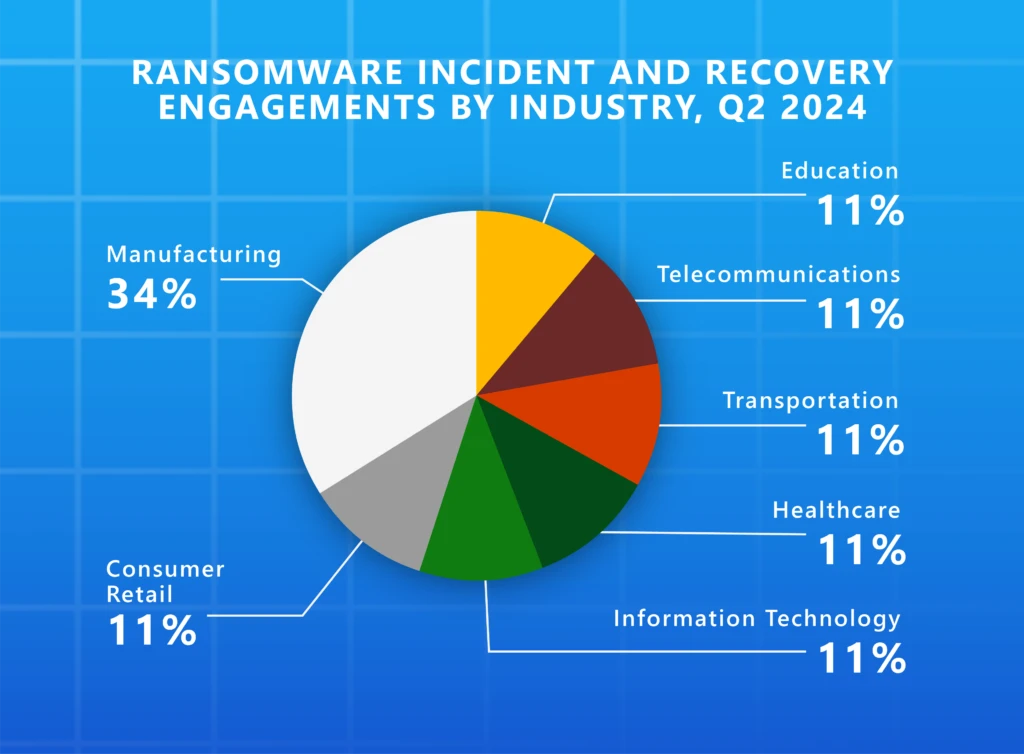
Education is also on the front lines confronting how adversaries test their tools and their techniques. According to data from Microsoft Threat Intelligence, the education sector is the third-most targeted industry, with the United States seeing the greatest cyberthreat activity.
Cyberthreats to education are not only a concern in the United States. According to the United Kingdom’s Department of Science Innovation and Technology 2024 Cybersecurity Breaches Survey, 43% of higher education institutions in the UK reported experiencing a breach or cyberattack at least weekly.²
QR codes provide an easily disguised surface for phishing cyberattacks
Today, quick response (QR) codes are quite popular—leading to increased risks of phishing cyberattacks designed to gain access to systems and data. Images in emails, flyers offering information about campus and school events, parking passes, financial aid forms, and other official communications all frequently contain QR codes. Physical and virtual education spaces might be the most “flyer friendly” and QR code-intensive environments anywhere, given how big a role handouts, physical and digital bulletin boards, and other casual correspondence help students navigate a mix of curriculum, institutional, and social correspondence. This creates an attractive backdrop for malicious actors to target users who are trying to save time with a quick image scan.
Recently the United States Federal Trade Commission issued a consumer alert on the rising threat of malicious QR codes being used to steal login credentials or deliver malware.³
Microsoft Defender for Office 365 telemetry shows that approximately more than 15,000 messages with malicious QR codes are targeted toward the educational sector daily—including phishing, spam, and malware.
Legitimate software tools can be used to quickly generate QR codes with embedded links to be sent in email or posted physically as part of a cyberattack. And those images are hard for traditional email security solutions to scan, making it even more important for faculty and students to use devices and browsers with modern web defenses.
Targeted users in the education sector may use personal devices without endpoint security. QR codes essentially enable the threat actor to pivot to these devices. QR code phishing (since its purpose is to target mobile devices) is compelling evidence of mobile devices being used as an attack vector into enterprises—such as personal accounts and bank accounts—and the need for mobile device protection and visibility. Microsoft has significantly disrupted QR code phishing attacks. This shift in tactics is evident in the substantial decrease in daily phishing emails intercepted by our system, dropping from 3 million in December 2023 to just 179,000 by March 2024.
Universities present their own unique challenges. Much of university culture is based on collaboration and sharing to drive research and innovation. Professors, researchers, and other faculty operate under the notion that technology, science—simply knowledge itself—should be shared widely. If someone appearing as a student, peer, or similar party reaches out, they’re often willing to discuss potentially sensitive topics without scrutinizing the source.
University operations also span multiple industries. University presidents are effectively CEOs of healthcare organizations, housing providers, and large financial organizations—the industry of industries factor, again. Therefore, top leaders can can be prime targets for anyone attacking those sectors.
The combination of value and vulnerability found in education systems has attracted the attention of a spectrum of cyberattackers—from malware criminals employing new techniques to nation-state threat actors engaging in old-school spy craft.
Microsoft continually monitors threat actors and threat vectors worldwide. Here are some key issues we’re seeing for education systems.
Email systems in schools offer wide spaces for compromise
The naturally open environment at most universities forces them to be more relaxed in their email hygiene. They have a lot of emails amounting to noise in the system, but are often operationally limited in where and how they can place controls, because of how open they need to be for alumni, donors, external user collaboration, and many other use cases.
Education institutions tend to share a lot of announcements in email. They share informational diagrams around local events and school resources. They commonly allow external mailers from mass mailing systems to share into their environments. This combination of openness and lack of controls creates a fertile ground for cyberattacks.
AI is increasing the premium on visibility and control
Cyberattackers recognizing higher education’s focus on building and sharing can survey all visible access points, seeking entry into AI-enabled systems or privileged information on how these systems operate. If on-premises and cloud-based foundations of AI systems and data are not secured with proper identity and access controls, AI systems become vulnerable. Just as education institutions adapted to cloud services, mobile devices and hybrid learning—which introduced new waves of identities and privileges to govern, devices to manage, and networks to segment—they must also adapt to the cyber risks of AI by scaling these timeless visibility and control imperatives.
Nation-state actors are after valuable IP and high-level connections
Universities handling federally funded research, or working closely with defense, technology, and other industry partners in the private sector, have long recognized the risk of espionage. Decades ago, universities focused on telltale physical signs of spying. They knew to look for people showing up on campus taking pictures or trying to get access to laboratories. Those are still risks, but today the dynamics of digital identity and social engineering have greatly expanded the spy craft toolkit.
Universities are often epicenters of highly sensitive intellectual property. They may be conducting breakthrough research. They may be working on high-value projects in aerospace, engineering, nuclear science, or other sensitive topics in partnership with multiple government agencies.
For cyberattackers, it can be easier to first compromise somebody in the education sector who has ties to the defense sector and then use that access to more convincingly phish a higher value target.
Universities also have experts in foreign policy, science, technology, and other valuable disciplines, who may willingly offer intelligence, if deceived in social-engineering cyberattacks employing false or stolen identities of peers and others who appear to be in individuals’ networks or among trusted contacts. Apart from holding valuable intelligence themselves, compromised accounts of university employees can become springboards into further campaigns against wider government and industry targets.
Nation-state actors targeting education

Peach Sandstorm has used password spray attacks against the education sector to gain access to infrastructure used in those industries, and Microsoft has also observed the organization using social engineering against targets in higher education.
Microsoft has observed a subset of this Iranian attack group targeting high-profile experts working on Middle Eastern affairs at universities and research organizations. These sophisticated phishing attacks used social engineering to compel targets to download malicious files including a new, custom backdoor called MediaPl.
Mabna Institute
In 2023, the Iranian Mabna Institute conducted intrusions into the computing systems of at least 144 United States universities and 176 universities in 21 other countries.
The stolen login credentials were used for the benefit of Iran’s Islamic Revolutionary Guard Corps and were also sold within Iran through the web. Stolen credentials belonging to university professors were used to directly access university library systems.

This North Korean group primarily targets experts in East Asian policy or North and South Korean relations. In some cases, the same academics have been targeted by Emerald Sleet for nearly a decade.
Emerald Sleet uses AI to write malicious scripts and content for social engineering, but these attacks aren’t always about delivering malware. There’s also an evolving trend where they simply ask experts for policy insight that could be used to manipulate negotiations, trade agreements, or sanctions.
Moonstone Sleet is another North Korean actor that has been taking novel approaches like creating fake companies to forge business relationships with educational institutions or a particular faculty member or student.
One of the most prominent attacks from Moonstone Sleet involved creating a fake tank-themed game used to target individuals at educational institutions, with a goal to deploy malware and exfiltrate data.

Storm-1877
This actor largely engages in cryptocurrency theft using a custom malware family that they deploy through various means. The ultimate goal of this malware is to steal crypto wallet addresses and login credentials for crypto platforms.
Students are often the target for these attacks, which largely start on social media. Storm-1877 targets students because they may not be as aware of digital threats as professionals in industry.
A new security curriculum
Due to education budget and talent constraints and the inherent openness of its environment, solving education security is more than a technology problem. Security posture management and prioritizing security measures can be a costly and challenging endeavor for these institutions—but there is a lot that school systems can do to protect themselves.
Maintaining and scaling core cyberhygiene will be key to securing school systems. Building awareness of security risks and good practices at all levels—students, faculty, administrators, IT staff, campus staff, and more—can help create a safer environment.
For IT and security professionals in the education sector, doing the basics and hardening the overall security posture is a good first step. From there, centralizing the technology stack can help facilitate better monitoring of logging and activity to gain a clearer picture into the overall security posture and any vulnerabilities.
Oregon State University
Oregon State University (OSU), an R1 research-focused university, places a high priority on safeguarding its research to maintain its reputation. In 2021, it experienced an extensive cybersecurity incident unlike anything before. The cyberattack revealed gaps in OSU’s security operations.
“The types of threats that we’re seeing, the types of events that are occurring in higher education, are much more aggressive by cyber adversaries.”
—David McMorries, Chief Information Security Officer at Oregon State University
In response to this incident, OSU created its Security Operations Center (SOC), which has become the centerpiece of the university’s security effort. AI has also helped automate capabilities and helped its analysts, who are college students, learn how to quickly write code—such as threat hunting with more advanced hunting queries.
Arizona Department of Education
A focus on Zero Trust and closed systems is an area that the Arizona Department of Education (ADE) takes further than the state requirements. It blocks all traffic from outside the United States from its Microsoft 365 environment, Azure, and its local datacenter.
“I don’t allow anything exposed to the internet on my lower dev environments, and even with the production environments, we take extra care to make sure that we use a network security group to protect the app services.”
—Chris Henry, Infrastructure Manager at the Arizona Department of Education
Follow these recommendations:
- The best defense against QR code attacks is to be aware and pay attention. Pause, inspect the code’s URL before opening it, and don’t open QR codes from unexpected sources, especially if the message uses urgent language or contains errors.
- Consider implementing “protective domain name service,” a free tool that helps prevent ransomware and other cyberattacks by blocking computer systems from connecting to harmful websites. Prevent password spray attacks with a stringent password and deploy multifactor authentication.
- Educate students and staff about their security hygiene, and encourage them to use multifactor authentication or passwordless protections. Studies have shown that an account is more than 99.9% less likely to be compromised when using multifactor authentication.

Corey Lee has always had an interest in solving puzzles and crimes. He started his college career at Penn State University in criminal justice, but soon realized his passion for digital forensics after taking a course about investigating a desktop computer break-in.
After completing his degree in security and risk analysis, Corey came to Microsoft focused on gaining cross-industry experience. He’s worked on securing everything from federal, state, and local agencies to commercial enterprises, but today he focuses on the education sector.

After spending time working across industries, Corey sees education through a different lens—the significantly unique industry of industries. The dynamics at play inside the education sector include academic institutions, financial services, critical infrastructure like hospitals and transportation, and partnerships with government agencies. According to Corey, working in such a broad field allows him to leverage skillsets from multiple industries to address specific problems across the landscape.
The fact that education could also be called underserved from a cybersecurity standpoint is another compelling challenge, and part of Corey’s personal mission. The education industry needs cybersecurity experts to elevate the priority of protecting school systems. Corey works across the public and industry dialogue, skilling and readiness programs, incident response, and overall defense to protect not just the infrastructure of education, but students, parents, teachers, and staff.
Today, Corey is focused reimagining student security operations centers, including how to inject AI into the equation and bring modern technology and training to the table. By growing the cybersecurity work force in education and giving them new tools, he’s working to elevate security in the sector in a way that’s commensurate with how critical the industry is for the future.
Next steps with Microsoft Security
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us on LinkedIn (Microsoft Security) and X (@MSFTSecurity) for the latest news and updates on cybersecurity.
¹Global Cyberattacks Continue to Rise with Africa and APAC Suffering Most, Check Point Blog. April 27, 2023.
²Cyber security breaches survey 2024: education institutions annex, The United Kingdom Department for Science, Innovation & Technology. April 9, 2024
³Scammers hide harmful links in QR codes to steal your information, Federal Trade Commission (Alvaro Puig), December 6, 2023.
Methodology: Snapshot and cover stat data represent telemetry from Microsoft Defender for Office 365 showing how a QR code phishing attack was disrupted by image detection technology and how Security Operations teams can respond to this threat. Platforms like Microsoft Entra provided anonymized data on threat activity, such as malicious email accounts, phishing emails, and attacker movement within networks. Additional insights are from the 78 trillion daily security signals processed by Microsoft each day, including the cloud, endpoints, the intelligent edge, and telemetry from Microsoft platforms and services including Microsoft Defender. Microsoft categorizes threat actors into five key groups: influence operations; groups in development; and nation-state, financially motivated, and private sector offensive actors. The new threat actors naming taxonomy aligns with the theme of weather.
© 2024 Microsoft Corporation. All rights reserved. Cyber Signals is for informational purposes only. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED OR STATUTORY, AS TO THE INFORMATION IN THIS DOCUMENT. This document is provided “as is.” Information and views expressed in this document, including URL and other Internet website references, may change without notice. You bear the risk of using it. This document does not provide you with any legal rights to any intellectual property in any Microsoft product.