The not-for-profit sector is one of Australia’s biggest employers and revenue sources. 1.4 million people work in the not-for-profit sector in Australia, and another 3.2 million people volunteer. The overall revenue of the sector is $190 billion, and that money goes directly into supporting critical causes across the country.
Unfortunately, according to new research by Infoxchange, the sector is ill-equipped to handle the security requirements of modern IT environments, and that is not only putting close to five million people at risk, but it’s also inhibiting the NFP sector’s ability to address Australia’s most pressing humanitarian and social justice challenges.
Jump to:
NFP cyber security insights from Infoxchange
Infoxchange’s Digital Technology in the Not-For-Profit Sector offers a deep dive into the dominant trends facing charities and nonprofits with technology, based on a survey of more than 1,000 organisations in the sector. Insights include:
- One in eight surveyed organisations had experienced a cyber security incident in the past year.
- Only 23% had effective information security processes in place, allowing staff and volunteers to safeguard the organisation’s data.
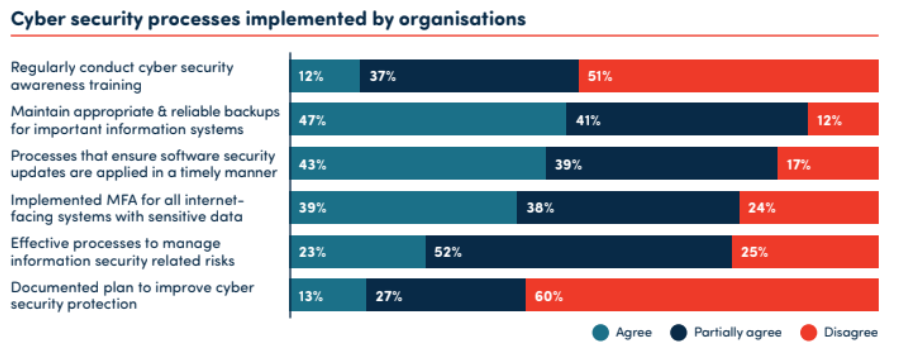
- Just 39% had implemented multi-factor authentication for internet-facing systems with sensitive data, while a mere 13% had a documented plan to improve cyber security protection.
- A mere 12% of NFPs conducted regular cyber security awareness training, and only one in five had a cyber security policy in place.
These NFPs do understand the importance of digital modernisation. Elsewhere in the report, 45% said they had already moved the “majority” of their IT to the cloud. NFPs are also deeply interested in the potential for technology to enhance their communications, with 38% saying that improving their website was their key priority looking forward. Meanwhile, 32% said that making better use of digital marketing was the main technology goal.
Lack of support leaves NFPs with poor security practices
And yet with no cyber security question did the majority “agree” that they were operating according to best practices (Figure A).
Figure A
“Despite this massive footprint in our economy and in our lives, charities and not-for-profits have not been provided with the support they need to deal with an increasingly sophisticated level of cyber attacks,” said David Crosbie and Tim Costello AO, from the Community Council for Australia, in a joint statement. “Unlike businesses, charities spend every spare dollar they can find on serving their communities.
“Allocating more resources to strengthen cyber security would mean reducing the level of services available in our communities. Many charities and NFPs struggle to withdraw services, even though cyber security is clearly an important priority.”
The impact of poor security
In August, news broke that the data of as many as 50,000 donors — affecting up to 70 NFPs, including major charities such as Fred Hollows Foundation, Cancer Council and Canteen — had been leaked and published on the dark web.
This was due to the NFPs partnering with the wrong organisation — in this case, Pareto Phone for telemarketer services — but it highlights the low levels of security concern or awareness among many charities.
Organisations are obliged to ensure third-party partners are responsible shepherds for customer data.
Separately, in 2022, another major Australian charity, The Smith Family, was targeted directly by hackers and had critical data of around 80,000 donors, including credit card and personal information, stolen.
NFP’s lack of security awareness is exposing themselves to legal liability
As noted by Moores, a legal firm that specialises in supporting charities and other “social good” organisations, the impacts of cyber breaches on NFPs are particularly damaging.
SEE: Australian enterprises are taking an “assume-breach” approach to cyber security.
“Unfortunately, many charities and NFPs are susceptible to cyber security attacks due to low levels of cyber resilience,” the firm noted in a blog. “For a charity or NFP, failing to take appropriate action to secure data could mean: The exposure of sensitive information of beneficiaries, donors or members; the loss of charity funds and resources; reputational damage; and breach of legal obligations.”
And yet, despite these concerns and the difficulties NFPs face in financing security, there appears to be little effort on any level to address the challenge.
For example, the Community Council for Australia is using Infoxchange’s report to lobby the Prime Minister, claiming that the 2023–2030 Australian Cyber Security Strategy discussion paper (including the “six shields” concept) fails to specifically acknowledge charities and not-for-profits, despite their significant contributions to the Australian workforce, GDP and community well-being.
“It has never been more important to build the digital capabilities and resilience of the not-for-profit sector,” Infoxchange CEO David Spriggs said in a release, supporting the calls for more strategic and national support for NFPs and cyber security. “As Australians bear the brunt of the cost-of-living crisis, this is putting greater pressure on not-for-profits and local community organisations who are at the front line in responding to record levels of service demand.”
A back-to-basics approach
It is unlikely that NFPs are going to see a sudden influx of budget to improve their security position. In lieu of that, IT professionals working in NFPs should adopt a “back-to-basics” approach to IT security and make sure that, at the very least, organisations are following these best practices.
Educate and train staff
The first line of defence in cyber security is often the users themselves. IT pros should conduct regular training sessions to educate staff about the latest cyberthreats and how to recognize them. This includes phishing scams, malware and ransomware attacks.
Implement strong password policies
One area where there is strong awareness among NFPs is in the value of strong password and password management policies that include two-factor and multi-factor authentication. IT pros should be looking to roll out the most robust zero-trust policies possible, especially for those NFPs that are operating predominantly in the cloud.
Regularly update and patch systems
Cyberthreats are constantly evolving, and outdated software can have vulnerabilities that hackers can exploit. Regularly updating and patching all systems is crucial to keeping them secure.
PREMIUM: Take advantage of this patch management policy.
Install and update security software
Use reliable security software that offers real-time protection against malware and other cyberthreats. Many modern security software packages have artificial intelligence built in, which is critical to leverage when human resources are scarce.
Back up data regularly
Regular data backups are essential for recovering from cyberattacks. Backups should be made frequently and tested regularly to ensure they can be restored if needed. It’s also important to store backups securely, either off-site or in the cloud, to protect against physical damage or theft. As a defence against ransomware, security teams should be looking for backups that have an “air gap,” too, preventing the ransomware from reaching the backup data.
Invest in managed services
NFPs should consider investing in managed services to support their internal teams. The security upshot to moving work into the cloud is that security teams can support the organisation remotely, and many MSPs with a security bent do specialise in supporting small and under-resourced organisations.